Quick Links
Other Products
CryptoLicensing
Add licensing, copy-protection and activation capabilities to your apps, libraries and websites using latest military strength cryptographic technology.
Visual Build Automation, Testing, Deployment And Release Management Software.
Crypto Logger
.Net Edition
Flexible high-performance logging library + powerful easy-to-use console
to view, search, manage and analyze log data.
Develop namespace extensions in .Net fast and painlessly!
Develop namespace extensions using MFC, ATL or plain C++ fast and painlessly!
Develop IE toolbars, explorer bars, desk bands and all shell extensions in .Net fast and painlessly!
Develop IE toolbars, explorer bars, desk bands and all shell extensions in MFC, ATL or plain C++ fast and painlessly!
Windows Explorer-Like File And Folder Browsing Inside Of Visual Studio.
8 Ways To Protect And Obfuscate Your .Net Code Against Reverse-Engineering Using Crypto Obfuscator
Introduction
Most non-.Net compilers emit binary programs containing native CPU instructions which are very hard to disassemble, decompile and reverse-engineer. However, all .Net compilers such as C#, VB.Net, Managed C++, IronPyhton, etc emit compiled programs in MSIL (Microsoft Intermediate Language) format. This format preserves a lot of high-level information about your software such as class, field, method, property and parameter names and even the actual code in a well-defined structure. This has facilitated the development of many decompilers and dissassemblers which can extract this information from a .Net assembly. Some tools can even reconstruct the actual structure of your code including loops, if statements, method calls, etc. Needless to say, this means that an unprotected .Net assembly is an easy target for hackers, crackers or competitors who can easily reverse-engineer your .Net code from the compiled assembly. They can easily glean valuable trade secrets, algorithms, sensitive information such as passwords, SQL queries, etc stored in strings, or even try to find security vulnerabilities and change product functionality.
Obfuscation & Protection Techniques
All is not lost however as there exist various methods and techniques which makes it extremely difficult for a hacker, cracker or competitor to reverse-engineer your application. Crypto Obfuscator makes use of the following advanced and sophisticated obfuscation and protection techniques:
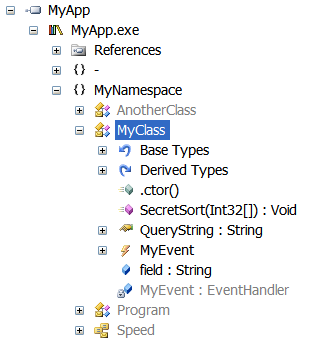
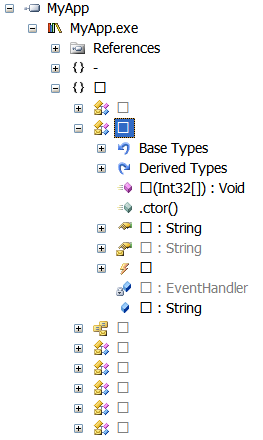
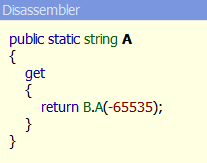
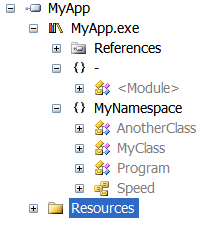
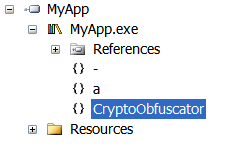
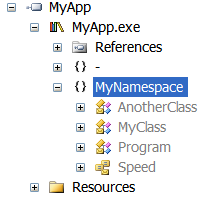
Symbol Renaming
Crypto Obfuscator renames the names of the classes, methods, properties, fields, events, etc in your .Net assembly to a garbled unintelligible name. Depending on the symbol renaming scheme chosen, this will result in either very long or very short names which have no relation to the original names. The original names cannot be derived or guessed from the obfuscated names. Since meaningful names are the most powerful ally when reverse-engineering a software, this makes it very hard to determine the purpose and function of the renamed entity.
| Before
|
After
|
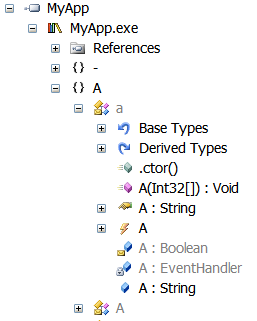
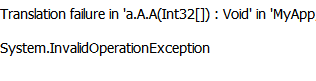
Advanced Overload Renaming
Crypto Obfuscator renames fields or methods with different signatures to the same name. For example two fields having types int and boolean will be given the same name. Similarly two methods will different parameters will be given the same name. In the case of methods, the method return type is also used in the signature even though high-level languages such as C# and VB.Net do not support overloading by return type. The .Net runtime is able to differentiate between the fields/methods without any problem since the signatures are different. Needless to say, this scheme makes it even harder to reverse-engineer your code.
| Before
|
After
|
Download Your Free Trial Now or Buy Now | Have a question? Email us
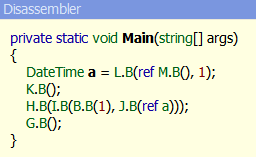
Method Call Hiding
Crypto Obfuscator can hide calls to methods and properties from external assemblies such as those from the .Net framework. In addition, it can also do the same for unrenamed methods and properties from the assemblies which are being obfuscated. This provides very strong obfuscation and makes it impossible to determine when, where and how such methods and properties are used.
| Before
|
After |
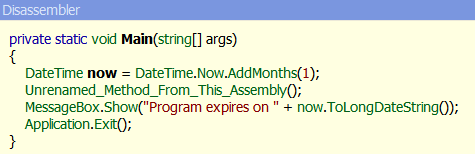
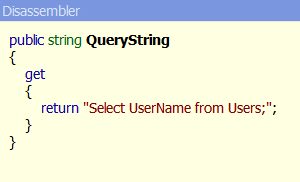
String Encryption
.Net assemblies contain all the literal strings used in your code in plain view for anybody to see. Literal strings often contain sensitive information such as login information, passwords, SQL queries, algorithm parameters. In addition, they also help in reverse-engineering your .Net code by providing a marker. For example, someone wanting to remove license checking from your software will search for all instances of strings like "license" or 'valid" or "invalid". Once they have found such strings, they will examine the surrounding code to see if it is the licensing checking code and if so, remove or disable it. Crypto Obfuscator solves all these issues by encrypting all literal strings in your .Net code.
| Before
|
After
|
Advanced Tamper Detection
Crypto Obfuscator can perform strong name verification of the assembly itself even if strong-name verification has been turned OFF on the machine on which the assembly is running or if the assembly has been registered in the verification 'skip-list' - this is typically done by hackers or crackers. Furthermore, the strong name verification is done using the original key used to sign the assembly when it was processed by Crypto Obfuscator. Thus, strong name verification fails even if the key is removed or replaced - again something typically done by hackers or crackers.
Download Your Free Trial Now or Buy Now | Have a question? Email us
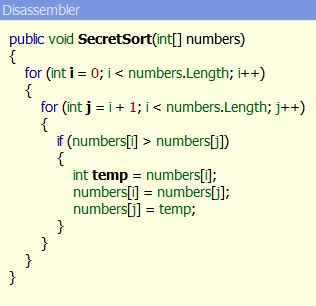
Control Flow Obfuscation
In .Net assemblies, even the code is stored in a well structured manner using a published format. This enables a sufficiently advanced decompiler to reconstruct to a pretty accurate degree the exact structure of your code including the for/while loops, if statements, try-catch blocks, etc. When doing control flow obfuscation on your code, Crypto Obfuscator changes the structure of your code into spaghetti code while maintaining 100% the logic and output of the code. The result is that decompilers are unable to reconstruct your code and output incorrect or garbage code. Most of the times they crash while trying to do so. This provides powerful method body protection for your software.
| Before
|
After
|
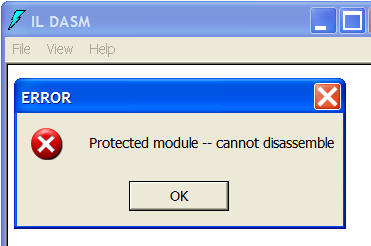
ILDASM Suppression
ILDASM (Microsoft IL Dissassembler) is a free tool to disassembly any .Net assembly into MSIL (Microsoft Intermediate Language) and extract the entire contents including the classes, methods, code and resources from the assembly. Crypto Obfuscator can modify the assembly in such a way that ILDASM refuses to disassemble the assembly.
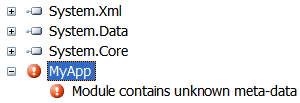
Anti-Reflection Protection
Many decompilers, dissassemblers and memory dumpers use .Net Reflection mechanism to extract information about a .Net assembly. Crypto Obfuscator can modify the assembly in such a way that such tools will fail when trying to work on your assembly.
| Before
|
After
|
Download Your Free Trial Now or Buy Now | Have a question? Email us
Anti-Decompiler Protection
Advanced decompilers such as the freely available .Net Reflector are your enemy in the battle against the hackers, crackers and competitors. Crypto Obfuscator can modify your assembly in such a way that such tools fail to work on your assembly - many times they are not even able to open your assembly, let alone examine it.
| Before
|
After
|
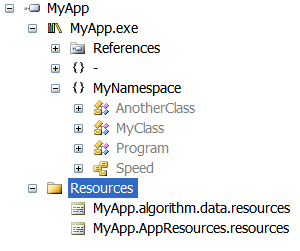
Resource Encryption
Tools such as ILDASM, .Net Reflector and others can easily extract resources from your assembly. Such resources often contain valuable, sensitive or copyrighted information such as images, UI (WPF baml files), textual content, etc. Crypto Obfuscator can hide and encrypt all such resources so that it is impossible to see them, let alone extract them from the assembly.
| Before
|
After
|
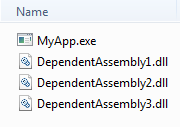
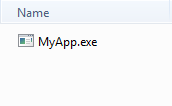
Assembly Encryption
Crypto Obfuscator can encrypt all dependant assemblies and any additional assemblies used by your software. This makes it impossible for someone to get their hands on individual assemblies. You can use this feature to your advantage by separating all sensitive or important code and data in a dependant assembly. In fact, this can be taken to an extreme - simply put ALL your code/data in a separate assembly and use a shell assembly as a starter/loader assembly for your application.
| Before
|
After
|
Conclusion
Each of the above techniques on their own are pretty powerful and effective against hackers, crackers and competitors. When combined and used together for the obfuscation and code protection of your .Net assembly, they form an impenetrable shield which is extremely difficult to break. Even if broken into by the most expert of hands, all they will see are garbage, encrypted or obfuscated code, names and data.
Crypto Obfuscator arms .Net developers with a powerful code protection and obfuscation tool which enable them to deploy their .Net software without fear of IP theft, reverse-engineering, hacking, cracking and piracy.
Download Your Free Trial Now or Buy Now | Have a question? Email us
Quick
Links
Crypto Obfuscator For .Net: -- More
Info -- Download -- Buy
CryptoLicensing: -- .Net
Edition --- MFC
Edition --- ActiveX
Edition
Hyper Build: -- More
Info -- Download -- Buy
Crypto Logger For .Net: -- More
Info -- Download -- Buy
EZNamespaceExtensions: -- .Net
Edition -- MFC Edition
EZShellExtensions: -- .Net
Edition -- MFC Edition
VS Explorer for Visual Studio: -- Info
-- Download
Support: -- Technical
Support -- Articles
-- Case Studies
Company: -- About
-- Contact
Copyright © 2007-2020 LogicNP Software.